Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Data Engineering
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Databricks
- Data Engineering
- Automation creation of Databricks Top Level Reposi...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-14-2022 08:42 AM
I'm looking to automate the creation of Top Level repositories in Databricks however isn't possible using cli or API if this repo is private repository(Azure DevOps Repository) because require setup the token in user setting.
databricks repos create \
--url https://<orgname>:<PAT_token>@dev.azure.com/<orgname>/<projectname>/_git/<reponame>; \
--provider azureDevOpsServices \
--path /Repos/Repository/<reponame> \
--debugThat's a problem because use a git command like git clone with the same structure works without problems.
git clone https://<orgname>:<PAT_token>@dev.azure.com/<orgname>/<projectname>/_git/<reponame>;Someone with any idea to solve this challenge?
Labels:
1 ACCEPTED SOLUTION
Accepted Solutions
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-21-2022 06:31 AM
We have API availabe for repos https://docs.databricks.com/dev-tools/api/latest/repos.html#operation/get-repos also we are currently supporting SP.
Step 1: As an admin Create a Service Principal
Use this API SCIM API 2.0 (ServicePrincipals) | Databricks on AWS
Related doc: https://docs.databricks.com/administration-guide/users-groups/service-principals.html
Step 2: As an admin create a Databricks token on behalf of the Service Principal
Use this API:
Token Management API 2.0 | Databricks on AWS
Related doc: https://docs.databricks.com/administration-guide/users-groups/service-principals.html
Step 3: Using the Service Principal Databricks Token call the Git Credentials API
Add the Git token via this API: Git Credentials API 2.0 | Databricks on AWS
Step 4: Invoke Repos APIs as service principal using the SPNs Databricks Token
Related stackoverflow questions: Databricks REST API call for updating branch error : User Settings > Git Integration to set up an Az...
5 REPLIES 5
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-19-2022 12:46 AM
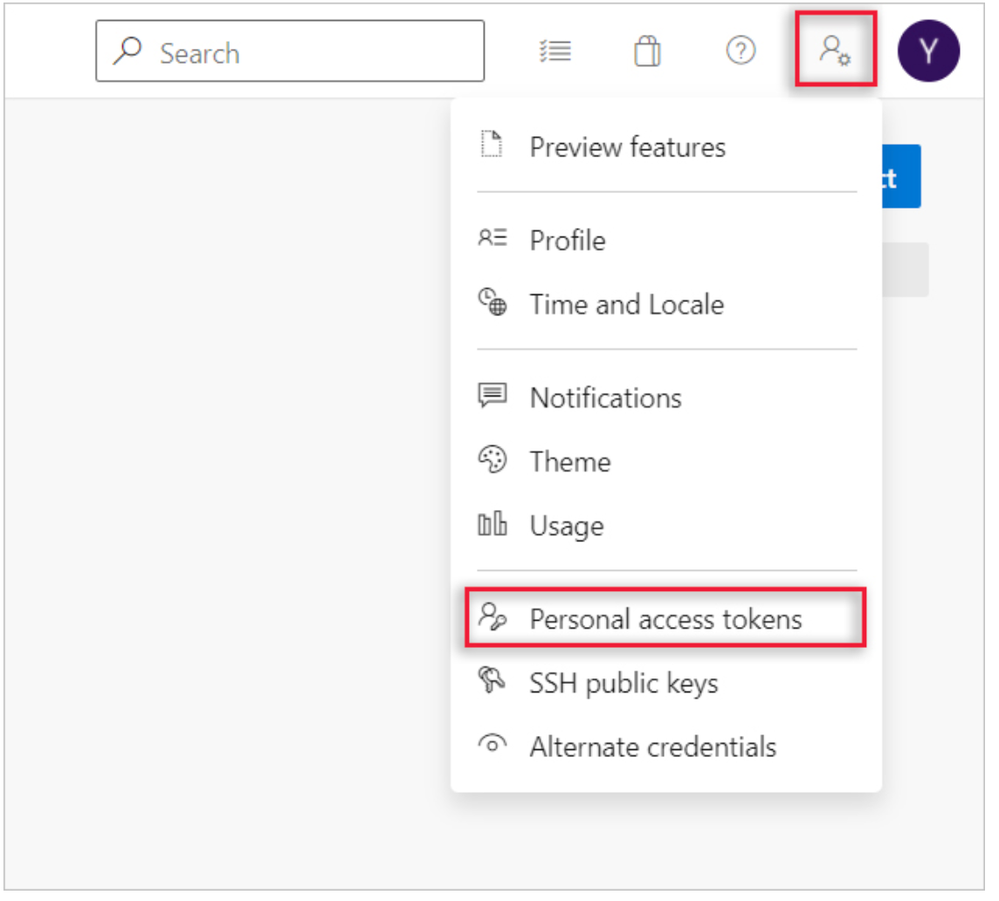
Hi @Luis Arias , Are you facing issues in creating a PAT?
To Create a PAT, Please follow the steps given in this article.
- Sign in to your organization (https://dev.azure.com/{yourorganization}).
- Open user settings from your home page and then select Personal access tokens.
- Select + New Token.
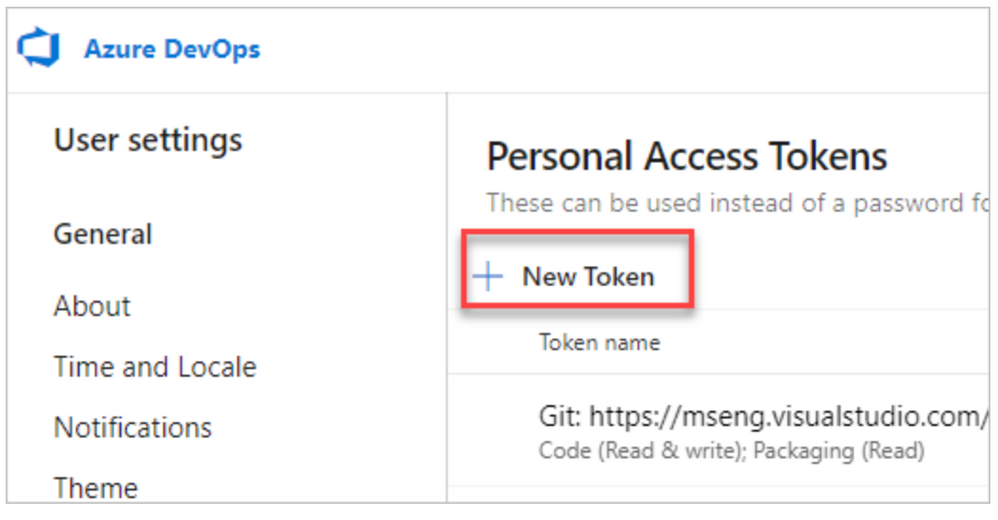
- Name your token, select the organization where you want to use the token, and then set your token to automatically expire after a set number of days.
Select the scopes for this token to authorize your specific tasks.
For example, to create a token to enable a build and release agent to authenticate to Azure DevOps Services, limit your token's scope to Agent Pools (Read & manage). To read audit log events, and manage and delete streams, select Read Audit Log, and then select Create.
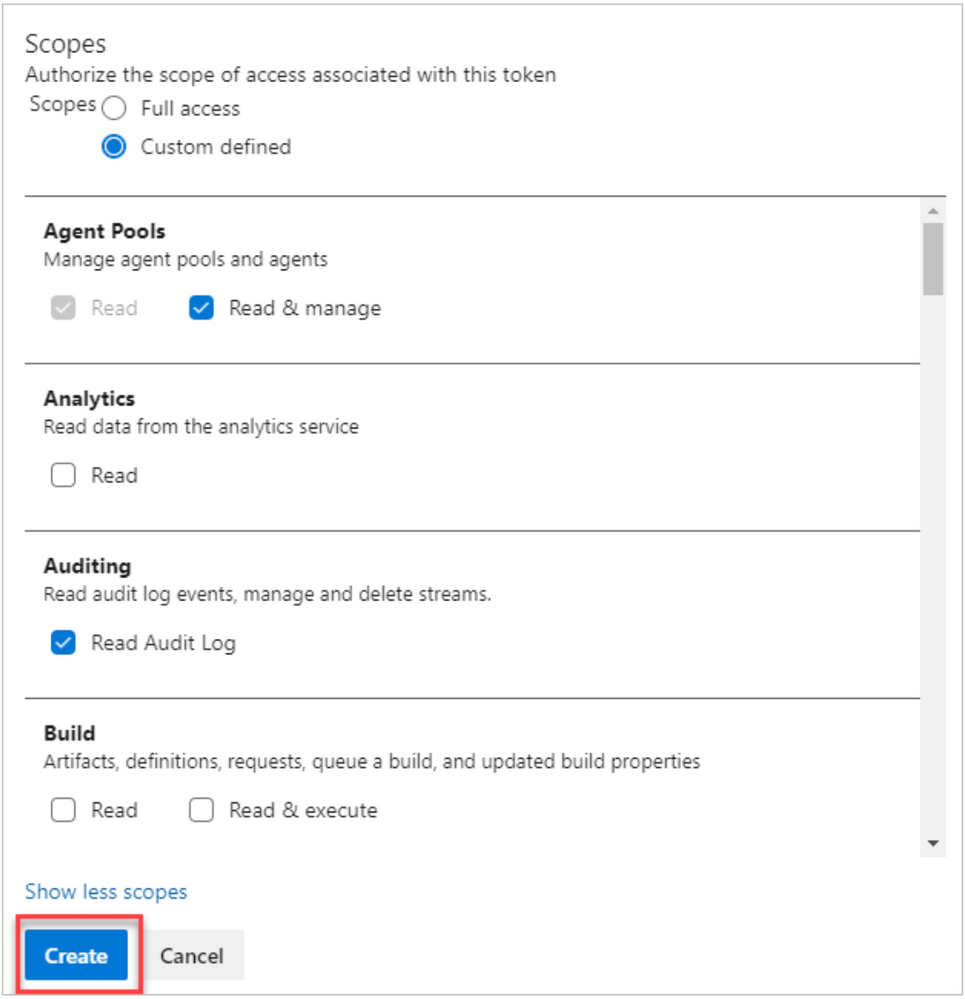
- When you're done, copy the token and store it in a secure location. For your security, it won't be shown again.
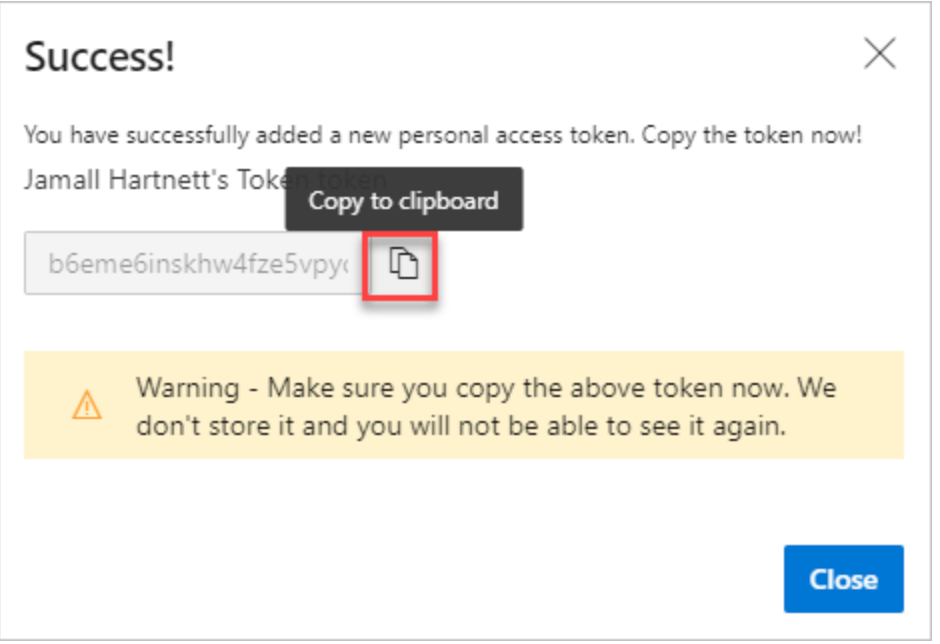
Warning:-
Treat and use a PAT like your password and keep it a secret.
Use your PAT anywhere your user credentials are required for authentication in Azure DevOps.
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-19-2022 03:04 AM
Thanks @Kaniz Fatma , I don't have problem creating PAT, the issue it's create the repo in databricks including the PAT.
PD: Take the consideration I don't wanna use Databricks user setting because everything it's deployed by command line.
Regards,
Luis
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-11-2022 04:39 AM
Hi @Luis Arias , I suppose you need to raise a feature request.
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-21-2022 06:31 AM
We have API availabe for repos https://docs.databricks.com/dev-tools/api/latest/repos.html#operation/get-repos also we are currently supporting SP.
Step 1: As an admin Create a Service Principal
Use this API SCIM API 2.0 (ServicePrincipals) | Databricks on AWS
Related doc: https://docs.databricks.com/administration-guide/users-groups/service-principals.html
Step 2: As an admin create a Databricks token on behalf of the Service Principal
Use this API:
Token Management API 2.0 | Databricks on AWS
Related doc: https://docs.databricks.com/administration-guide/users-groups/service-principals.html
Step 3: Using the Service Principal Databricks Token call the Git Credentials API
Add the Git token via this API: Git Credentials API 2.0 | Databricks on AWS
Step 4: Invoke Repos APIs as service principal using the SPNs Databricks Token
Related stackoverflow questions: Databricks REST API call for updating branch error : User Settings > Git Integration to set up an Az...
Options
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-13-2022 02:44 PM
Hi @Luis Arias,
Just a friendly follow-up. Did Atanu's response help you to resolved your question? please let us know
Welcome to Databricks Community: Lets learn, network and celebrate together
Join our fast-growing data practitioner and expert community of 80K+ members, ready to discover, help and collaborate together while making meaningful connections.
Click here to register and join today!
Engage in exciting technical discussions, join a group with your peers and meet our Featured Members.
Related Content
- Azure Devops repos access in Administration & Architecture
- Brickflow - An opinionated python framework to help build and deploy Databricks workflows at scale in Data Engineering
- Databricks deployment and automation tools comparison. in Administration & Architecture
- Support for setting R repository URLs in Databricks in Administration & Architecture
- Job Retry Wait Policy and Cluster Shutdown in Data Engineering